
Empowering People for ESG Progress: From Awareness to Action | SK Tes
Explore how ESG impact grows when organizations move beyond recognition and empower employees to contribute to strategy...

Why IT Leaders Must Prioritize Retired IT Hardware for Cyber Security
Learn why prioritizing the secure retirement of IT hardware is crucial for data security and compliance in today's...

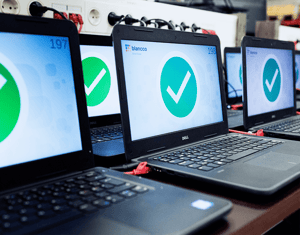
Ars Technica Visits SK Tes to Explore the Future of ITAD
Explore how SK Tes is redefining ITAD with data destruction, sustainability, and innovative lifecycle management in Ars...

Unlocking 150 Million Opportunities: Data Destruction at SK Tes
Discover how data destruction standards drive sustainability and emissions savings in data centers, transforming...
IEEE 2883-2022 Data Destruction Standards Explained | SK Tes
Explore IEEE 2883-2022—modern methods for secure data destruction: Clear, Purge, and Destruct explained...

8 Key Security Requirements for ITAD - Key Lessons by SK Tes
Response to Wisetek ITAD Theft - Ensure ITAD security with 8 key requirements to protect against data breaches and...

2024 Gartner® Market Guide for IT Asset Disposition (ITAD) | SK Tes
Gartner recognizes SK Tes as largest ITAD provider in 2024 Gartner Market Guide for IT Asset Disposition, highlighting...

The Vital Role of Cybersecurity & Best Practice in IT Asset Disposal
With growing digitization in business operations, cyber threats exposure is a high risk. What are best practices & how...

16 Key FAQs about onsite hard drive shredding
Shredding is the process of physically destroying your storage media or devices, irretrievably wiping all data. What...
%20(1).png?length=300&name=TESBlog%20(5)%20(1).png)
ITAD data security compliance: How ITAD company protects your data
Explore how ITAD companies achieve absolute data security throughout the IT asset disposition process and important...






.png?length=300&name=TESBlog%20(1).png)



